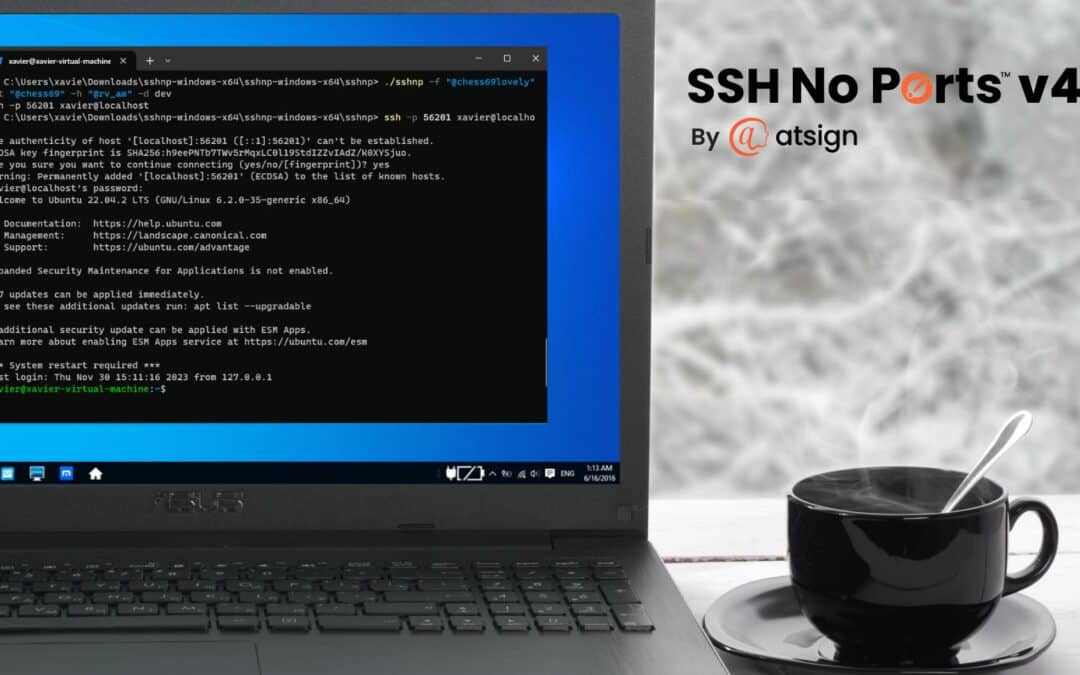
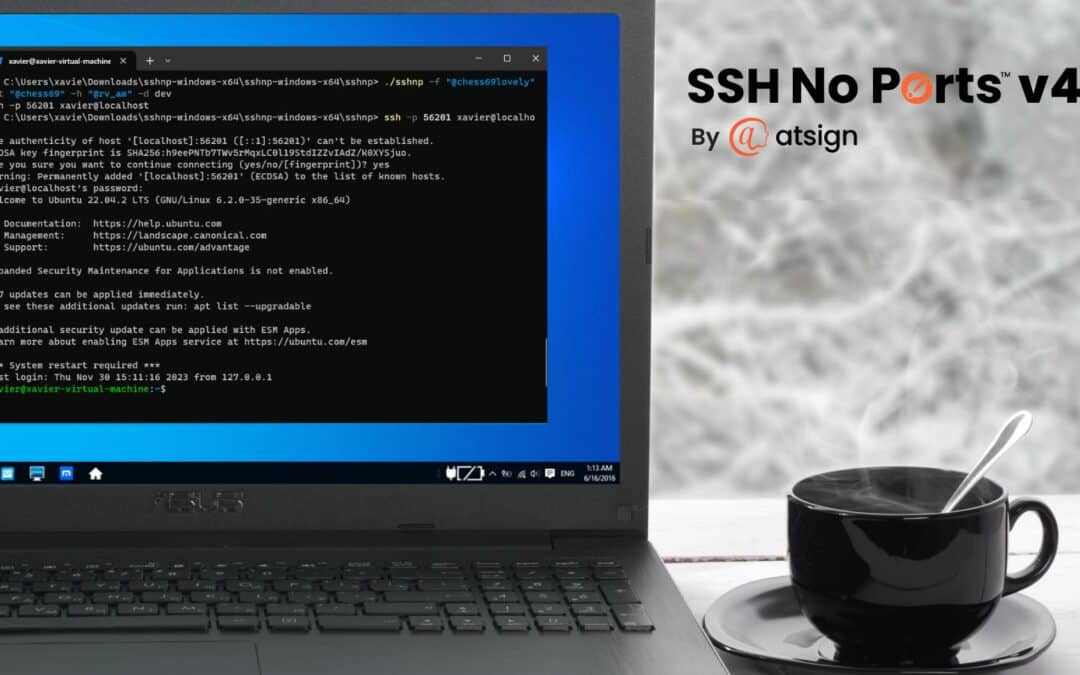

SSH No Ports Passes Pen Test
ARTICLE “No Dangerous Security Conditions”: SSH No Ports Passes Pen Test We Passed the Test SSH No Ports recently underwent penetration testing with leading cybersecurity firm, Fortis Cyber Security Limited. They used both manual and automated tools to...
Why Open Source
ARTICLE Atsign: Built on Open Source, Driven by Open Values From the very beginning, the founders of Atsign decided to make their software open source. There are many reasons for this, detailed below, but the fundamental reason was that open source reflects the values...
Secure Your Radio Station with Networking 2.0
ARTICLE Secure Your Radio Station Networking 2.0 keeps those radio waves free from interference If you don’t want your radio station to be hacked by a Scandinavian rock-music-loving hacker, then you need Atsign’s Networking 2.0 technology. After KRYZ Radio in...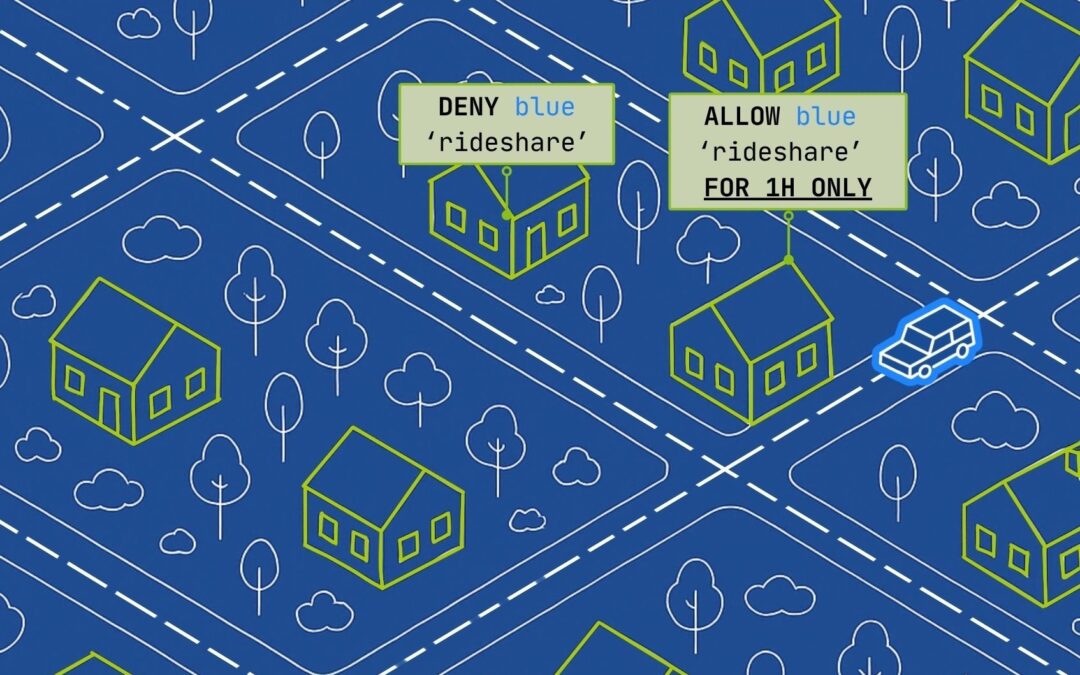
Understanding Picosegmentation for Network Security
ARTICLE Introducing Picosegmentation Microsegmentation was a good start—now let’s make it more secure and easier to maintain By Barbara Tallent The Introduction of Microsegmentation Microsegmentation was first introduced around 2014 by VMware. The idea was...
Recent Comments