Protect your Critical Infrastructure with the atPlatform™
Eliminate open port vulnerabilities and cryptographically secure every connection. The atPlatform is advanced protection for your critical infrastructure.
The atPlatform redefines critical infrastructure security with innovations that remove weak points and safeguard your systems against evolving threats.
Eliminates Attack Vectors and Threats
Removes open port vulnerabilities and protects the application layer, preventing unauthorized access and ensuring comprehensive security.
Keys Cut and Encrypted at the Edge
Cryptographic keys are generated and encrypted at the edge, ensuring data security from origin to destination.
True Zero Trust Architecture
Every connection is authenticated and verified, delivering maximum security without assumptions or shortcuts.
Check out our atSDK to learn how to quickly build products and services with reduced attack surface, end-to-end encryption and zero trust security built in.

For over 50 years, the internet’s client-server model has relied on open ports, creating massive attack surfaces vulnerable to exploitation. Atsign eliminates this reliance by removing the need for listening ports on devices that hold sensitive data or services. Using our patented, open-source technology, we enable secure, seamless communication for critical systems and organizations—without requiring a major infrastructure overhaul—redefining internet security at its core.
How Atsign Protects Critical Infrastructure
The atPlatform enables secure, private communication for critical infrastructure by eliminating open ports, using cryptographically verified addresses, and cutting keys at the edge for advanced privacy and security at scale.

NoPorts is a tool built on the atPlatform that delivers secure remote access by eliminating open ports and using cryptographically verified, end-to-end encrypted connections. It enables secure communication between devices in different locations while being simple, scalable, and built for critical systems.
How the atPlatform Outperforms Traditional Cybersecurity
How Atsign Defends Against Top Cyberattacks
Atsign’s proactive, security-first approach minimizes the risk of data breaches, improves customer trust, and significantly reduces both the long-term costs associated with monitoring and prevention tools and of repairing systems (and reputations) post-incident.
See how Atsign’s unique technology addresses today’s top cyber threats.
Featured Resources
The McKinsey AI Breach: How a Zero-Port Architecture Stops Autonomous Agents in Their Tracks
The McKinsey AI breach proved that legacy perimeter security is broken against autonomous AI agents. See the 4 steps of the machine-speed hack and why Atsign's Zero-Port Architecture would have stopped the attack instantly.
Where CEO Vision Meets CISO Approval: Launching AI Architect
AI Architect solves the enterprise AI bottleneck by combining visual architectural blueprints with a Zero Exposure foundation, allowing leaders to deploy secure, production-ready AI agents at 100x the speed of traditional coding.
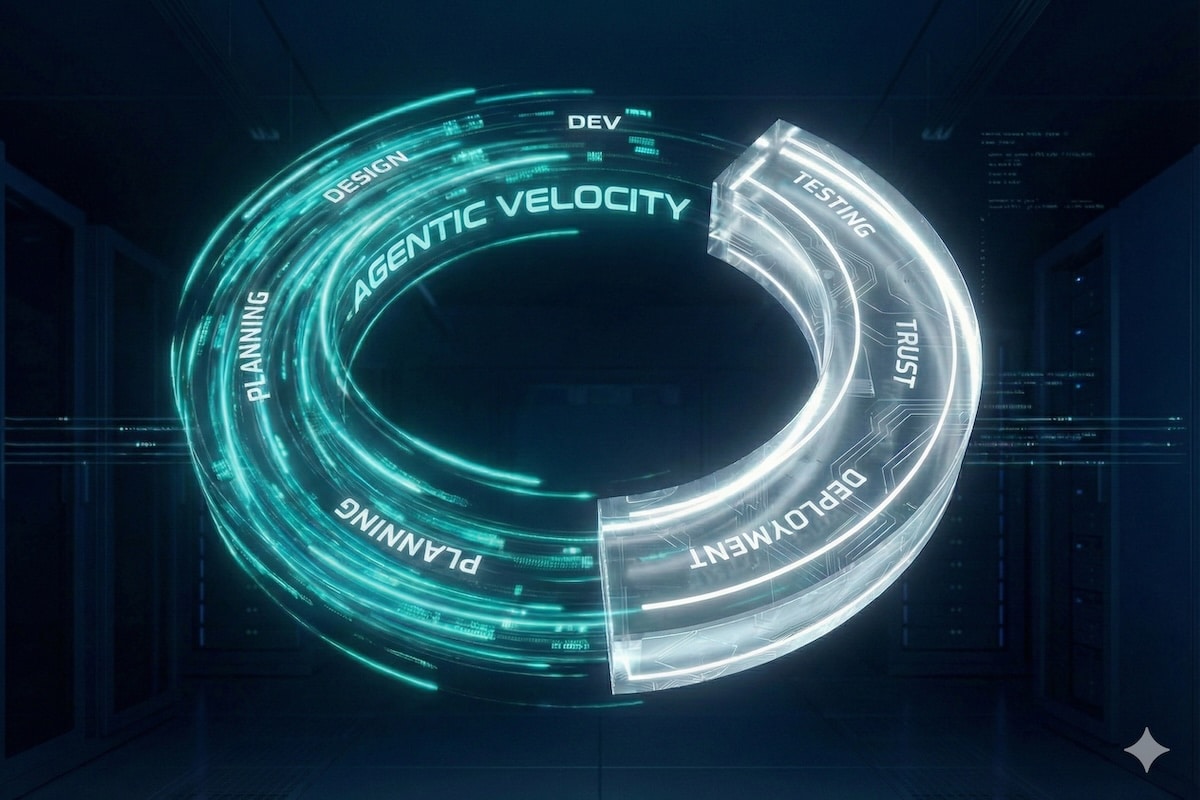
The SDLC is Broken: Building Architectural Trust for Agentic AI
The SDLC is broken. As AI moves from chatbots to autonomous agents, here is how the architecture of trust must change.