ARTICLE
Zero Trust You Can Actually Trust

There are a lot of companies out there advertising their security and privacy offerings. While we believe they are well-meaning, at the end of the day, they can still see your data–even if they pinky promise not to look at it.
So, why should you trust Atsign? Why is Atsign different from these other companies? Simply put, we can never–EVER–see your data!
What We Are About
Atsign’s award-winning technology is built using Networking 2.0 principles. Here are some important facets of our tech:
Open Source
- Anyone can view the source code and scrutinize, verify our claims, and even help improve the code.
Distributed and Peer-to-Peer
- Our tech does not rely on transmitting data through a centralized server; all information exchange is peer-to-peer, directly to the recipient’s private server, with no third-party snooping possible.
Cryptographically Secure
- Uses the tried and true, industry-standard encryption technologies we all know and trust.
Zero Trust
- Devices cut their own cryptographic keys right on the edge. Only the owner of the device and the intended recipient can ever see the data exchanged between them.
Testing the Tech
Crucially, we believe in rigorously testing our technology, not only in-house, but also from external and reputable organizations. Read more about how our technology (specifically, SSH No Ports) stood up to pen testing.
How secure is our code? We invite you to take a look. We have been using OpenSSF scorecards on all our key code repositories, and our scores are available for everyone to see. We take pride in our scores, and you will notice that our repositories rank among the best out there.
Here is a summary of our OpenSSF scores:
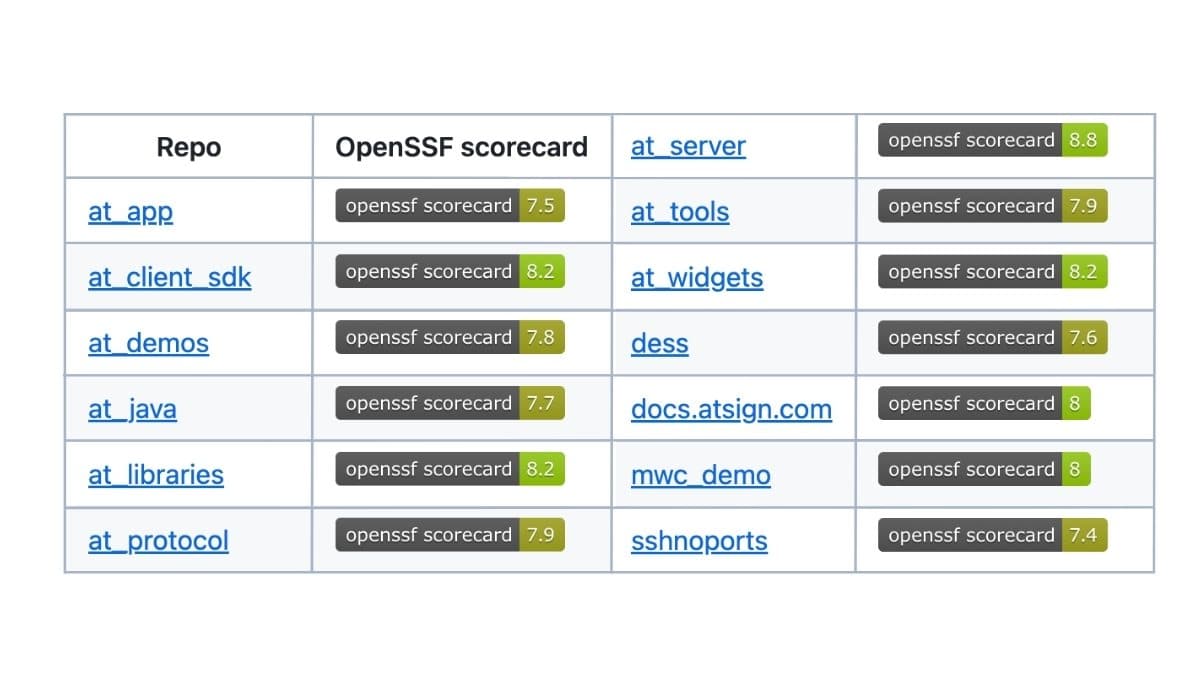
If you would like to learn more about OpenSSF, check out this blog post by Chris Swan who has been leading these efforts for us and also educating the community in the process through his various presentations, like this one from QCon in New York this past June.
The McKinsey AI Breach: How a Zero-Port Architecture Stops Autonomous Agents in Their Tracks
The McKinsey AI breach proved that legacy perimeter security is broken against autonomous AI agents. See the 4 steps of the machine-speed hack and why Atsign’s Zero-Port Architecture would have stopped the attack instantly.
Where CEO Vision Meets CISO Approval: Launching AI Architect
AI Architect solves the enterprise AI bottleneck by combining visual architectural blueprints with a Zero Exposure foundation, allowing leaders to deploy secure, production-ready AI agents at 100x the speed of traditional coding.
The SDLC is Broken: Building Architectural Trust for Agentic AI
The SDLC is broken. As AI moves from chatbots to autonomous agents, here is how the architecture of trust must change.
The MCP Security Paradox: Why the “USB-C for AI” Is an Architectural Minefield
Model Context Protocol promises universal connectivity for AI, but its current architecture is scaling a broken trust model that leaves sensitive enterprise data vulnerable to exploitation.
How to Let AI Agents Act on Your Behalf Without Losing Control
Imagine your AI agent rebooking a canceled flight and hotel while you sleep—securely. Learn how the atPlatform solves the trust and permission problems of AI, allowing agents to act for you while you maintain total control.