Atsign Technology for IoT Security & Simplicity
No Network Attack Surface
No Static IPs or Open Ports
No VPNs
No Firewalls
No Passwords
No Costly Security Budget
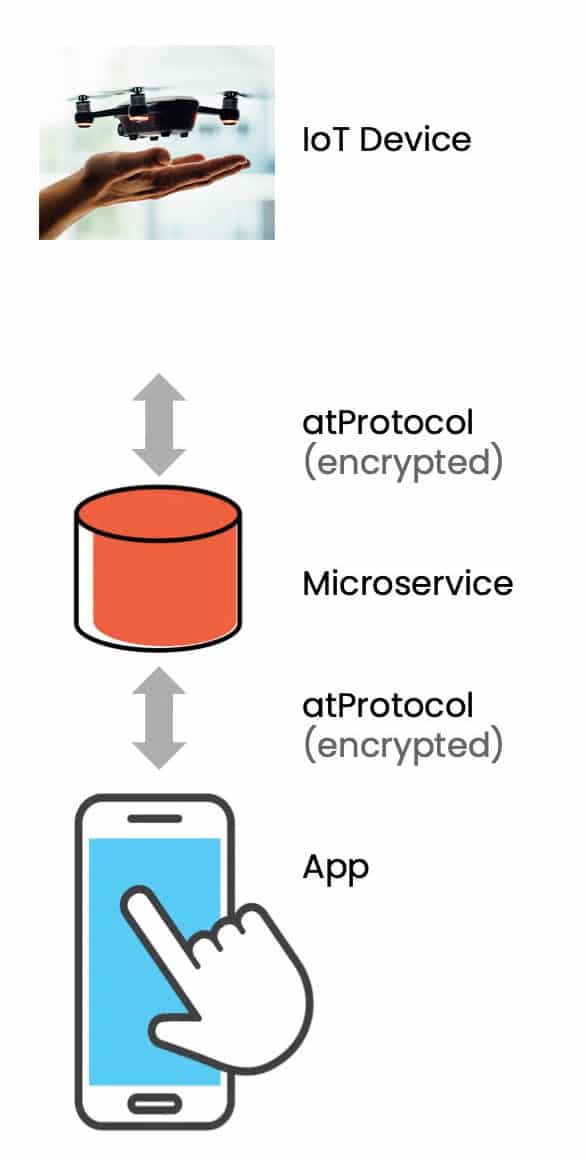
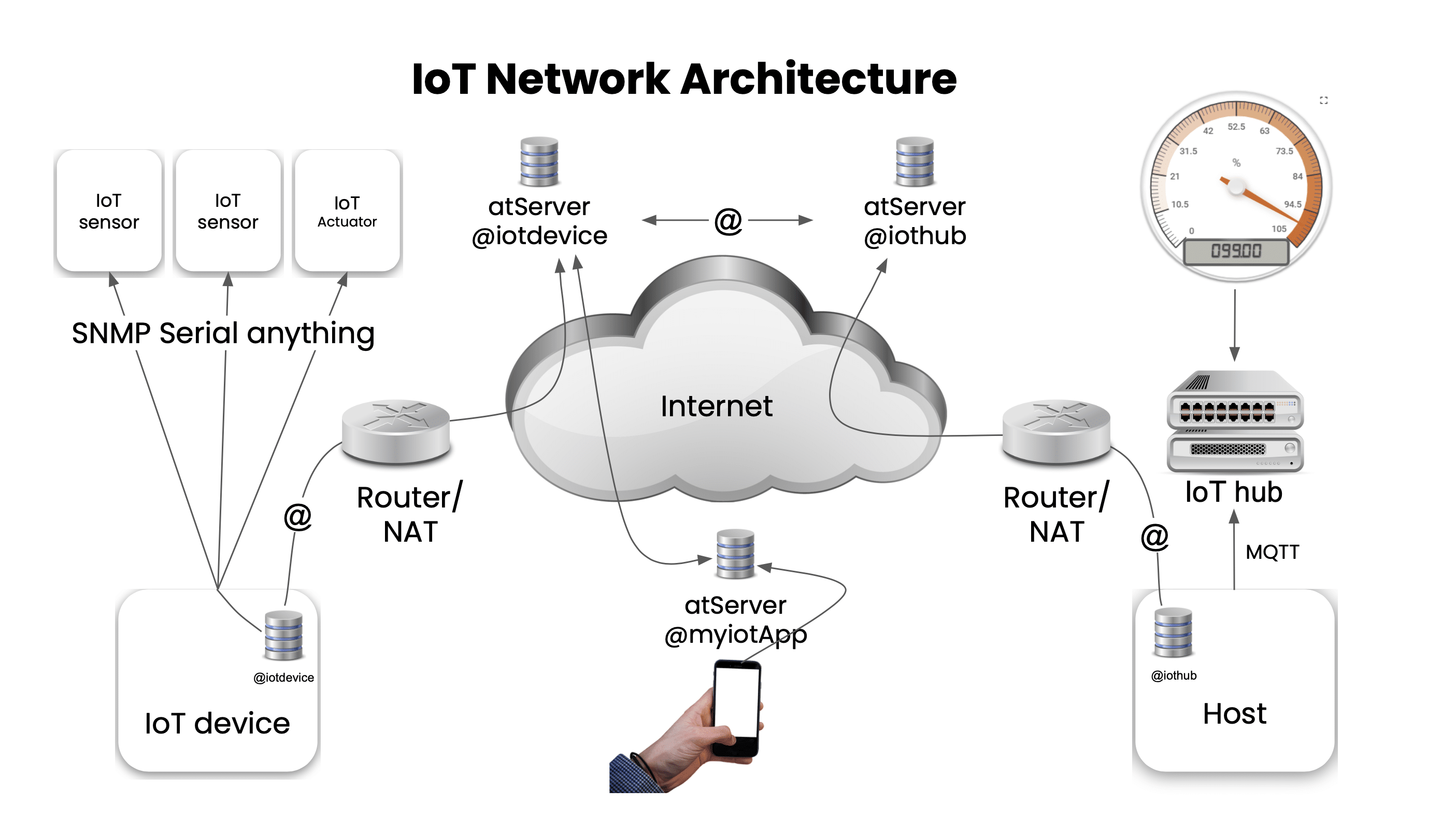
With Atsign Technology, every device is addressable through an atSign™, enabling end-to-end encrypted device communication.
Atsign Technology: Overview
IoT Security
As IoT (Internet of Things) devices become directly connected to the Internet via cellular, LoRaWAN, Wi-SUN, HaLOW, satellite, or Wi-Fi, better security, especially for the data they generate, becomes critically important. IoT security thinkers, including NIST IoT are working hard to solve this, but we believe that it requires a very different approach:
Instead of managing and protecting attack surfaces, we eliminate them.
Leading or contributing to IoT/OT? See how Atsign tackles key security challenges.
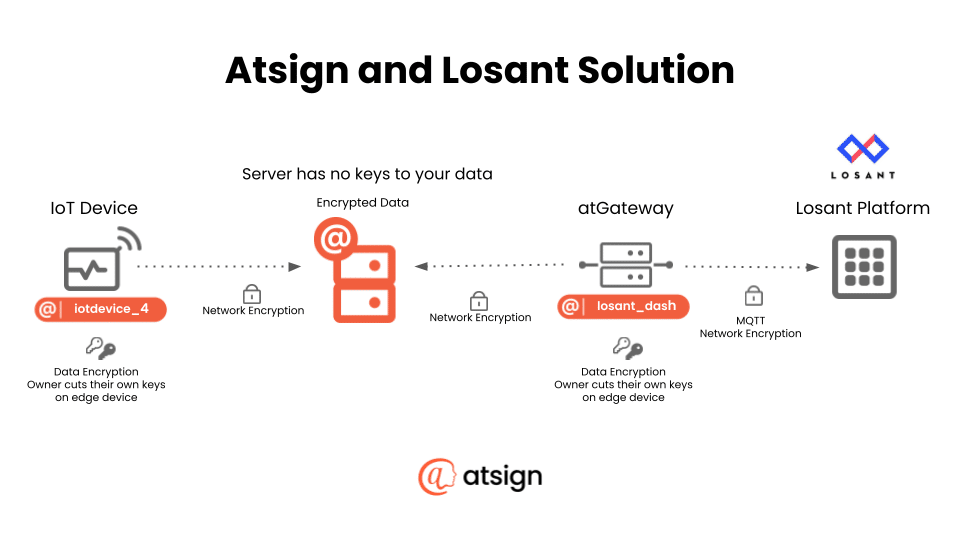
- Cryptographic keys are cut on the edge by the device
- A major attack surface is eliminated by removing the need for open ports on external interfaces
- Data is end-to-end encrypted, even when at rest
- Device owners can control which subset of data is sent to whom
IoT Simplicity
Atsign technology provides radical simplification for OT and IoT. We strip things down to the protocol level, creating both zero trust and zero configuration environments – completely without passwords – eliminating all attack surfaces created by over-complexity, and simplifying the administration of devices in the process.
Eliminates the need for physical security devices
- No firewalls required
- No VPNs required
- No open ports, including 22
- Provides data routing hardware lockdown of encryption keys
Makes devices easier to add and administer
- Fewer components required
- No complex administrative tools needed
Allows for dynamic IP addresses
- No longer need to assign static IPs
- Greatly simplifies network administration
Tools & Demos
IoT No Attack Surfaces: SSH No Ports Demo
- Create an SSH session on remote devices WITHOUT
- Configuring static IP addresses
- Installing complex VPNs
- Configuring complex firewalls
- Requiring TCP/IP ports open on device
- Zero attack surface
- Cryptographic authentication
- End-to-end encryption with RSA 4096 SSH session keys
Watch the demo!
Open-Source IoT with Dart and Flutter: The KRYZ Security Solution
The Problem: Radio station KRYZ was hacked by someone who started playing their own music.
The Solution: A Flutter application using the Atsign SDK that provides both security and real-time monitoring for the station.
We encourage you to take a look at the full walkthrough to see this groundbreaking tech for yourself. Better yet, request a demo from the man himself, here: iot@atsign.com
Watch the demo!
Resources
ZPE Systems & Atsign Partner for Zero Attack Surface Tech Solutions
This joint solution enables organizations to securely manage network infrastructure from anywhere in the world.
Losant and Atsign Partner to Offer Secure, Comprehensive IoT Solution
The partnership combines Losant's robust IoT platform with Atsign's security and privacy technology to provide businesses with a highly secure and scalable solution for managing their IoT devices and data.
ACA Pacific Partners with Atsign
ACA Pacific becomes an Atsign distributor in Singapore to deliver zero attack technology to secure the region’s growing IoT investments.
Complete Device Lockdown
Complete device lockdown is the future with SSH! No Ports, a tool that allows people to SSH into a device without having any ports open.
Atsign Honored as 2022 IoT Security Champion of the Year
Atsign honored as 2022 IoT Security Champion by the IoT Security Foundation.
IoT Cybersecurity Using the atPlatform
The atPlatform offers a simple and cost-effective way for IoT device manufacturers to secure their connected devices.
Atsign Zero Trust
Developing apps for a Zero Trust environment? The open-source atPlatform offers a simple and secure way to build IoT applications.
ZARIOT Recognized as Gold Winner in 2022 Future Digital Awards
Congrats to our partner, ZARIOT, on their win! Read about how the atPlatform helped them do it.
The Tale of a Smart City (IoT Smart Cities)
Panel discussion with our very own Gary Casey
IoT Security at Scale with Atsign
Here's how the atPlatform makes IoT security simple, complete, and scalable.
Atsign IoT
Here's how Atsign Technology helps IoT devices easily and safely connect to the Internet.
SSH No Ports: Secure Remote Access, No Open Ports
Introducing SSH No Ports, a utility that allows an administrator to securely access a remote device, without having any network ports open. No more pain, no more ports, no more network attack surface!
Simple, Efficient Privacy & Security for the Holistic IoT Solution
ZARIOT and Atsign have partnered to provide an important step forward in securing the IoT industry.
The atPlatform: A brief overview
Learn how the atPlatform deals with the replication of your data across the Internet, where everyone else owns it, except you.
How can Atsign help your organization?
Set up a call with someone from our team.