ARTICLE
4 Main Difficulties of Managing Gateways at Scale and How NoPorts Can Make Them Disappear
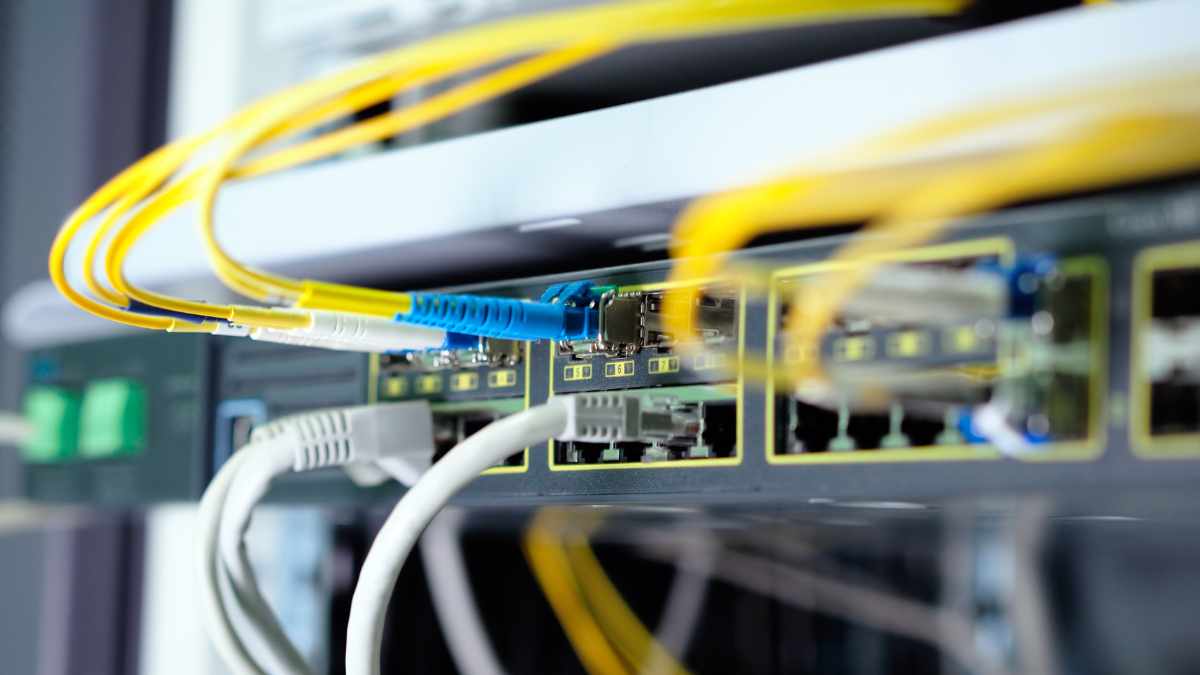
The Internet of Things (IoT) is rapidly expanding, and with it the number of gateways that are needed to connect devices to the internet. While gateways can perform a wide variety of services, their main job is to translate the data from IoT devices into a format that can be sent over the Internet, and vice versa.
Managing powerful and complex gateways at scale is a daunting task thanks to a number of challenges that need to be addressed, including,
- Addressability and reachability
- Security
- Data Privacy
- Cost
Let’s take a look at each:
Addressability
You need to be able to access your gateways to reconfigure them, perform updates, and to verify that all is well with them. Truck rolls—going to their location to access them physically—are expensive, so aren’t an option at scale. Remote access is required, which means gateways need to be addressable.
If the gateway is sitting directly on the Internet, that means it has to have a static (and public) IP address; this is fine when you’re dealing with one or two, but when you’re managing a few hundred, it quickly becomes prohibitively expensive and complicated, and it opens up some serious security risks (more about that in the next section).
Instead, many gateways are connected to a private backhaul network. More often than not, you don’t own the backhaul network, and must talk to the network’s firewall administrator for access. Approval can take weeks, or even months. In the case of a cellular backhaul network, it’s actually considered impossible to get access to a device because devices have dynamic IP addresses, or they are on a 1918 address which is unroutable. This leaves you without access.
For these reasons, organizations with deep pockets are setting up private 5G networks, which are prohibitively expensive, and can take several months, sometimes a full year, to deploy.
Security
Gateways have access to sensitive data and are often connected to the internet with open listening ports, making them a target for cyberattacks.
Firewalls are the de facto standard for protecting gateways. However, firewalls are complex devices that are painful to configure and manage. They often have a wide range of features and options, which can make it difficult to choose the right settings. If misconfigured, they are easy to exploit by attackers.
Data Privacy
Gateways generally use MQTT over TLS to encrypt data during transport. If the data is sent to the cloud, whoever owns the TLS certificate can see your data in the clear. To combat this, many organizations set up VPNs. Like firewalls, VPNs are also complex and difficult to set up and manage, and when misconfigured, they can provide another attack surface for cybercriminals.
Cost
The capital costs for the layers of software and networking necessary to keep gateways addressable, secure, and private are substantial and wrought with security risks, but they pale in comparison to the operating costs. Highly specialized personnel are required to set up and maintain gateways, firewalls, VPNs, and private 5G networks. These trained professionals are not inexpensive.
Additionally, every time you roll out another gateway, you need to hire a quarter of a person, a tenth of a person, or even a fiftieth of a person to manage it. This can quickly add up, making the operating costs of gateways prohibitive for many organizations.
NoPorts – Offering Relief from Scaling Difficulties
NoPorts makes anything addressable, with clear data ownership and control, allows contextual responses, and is inherently private and cryptographically secure.
Here are some of the ways NoPorts helps overcome scaling challenges:
- Makes gateways (and other devices) addressable and fully reachable wherever they are located—even on cellular networks—as long as they have outbound access to the internet. See our demo of SSH No Ports with a LoRaWAN gateway.
- Secures gateways by not requiring them to have any open ports to transmit data. Thus, there’s no need for firewalls or their nasty configurations.
- Encrypts data from the gateway in a way that only the intended recipients can access. This means that you can connect your gateway to the public internet in the most convenient way without needing VPNs or private 5G, and know that your data is safe.
- Lowers capital and operating costs by removing the need for firewalls, VPNs, or private 5G networks to protect devices and data. With all the layers of complexity removed, the number of gateways that your highly-trained professionals can manage goes up exponentially, saving a lot of money.
Eliminating attack surfaces, end-to-end encryption, addressability and reachability for gateways – no matter where they reside – sounds impossible, but it’s already here! For more information, visit noports.com.
Beyond Zero Trust: Anthropic’s Mythos and the Shift to Zero Exposure
If your AI agent gets tricked by a prompt injection, a firewall won’t stop the data leak—but a cryptographic kill switch will.
Why the ChatGPT Leak Proves We Need a Zero-Trust Harness for AI Agents
If your AI agent gets tricked by a prompt injection, a firewall won’t stop the data leak—but a cryptographic kill switch will.
The McKinsey AI Breach: How a Zero-Port Architecture Stops Autonomous Agents in Their Tracks
The McKinsey AI breach proved that legacy perimeter security is broken against autonomous AI agents. See the 4 steps of the machine-speed hack and why Atsign’s Zero-Port Architecture would have stopped the attack instantly.
Where CEO Vision Meets CISO Approval: Launching AI Architect
AI Architect solves the enterprise AI bottleneck by combining visual architectural blueprints with a Zero Exposure foundation, allowing leaders to deploy secure, production-ready AI agents at 100x the speed of traditional coding.
The SDLC is Broken: Building Architectural Trust for Agentic AI
The SDLC is broken. As AI moves from chatbots to autonomous agents, here is how the architecture of trust must change.